-
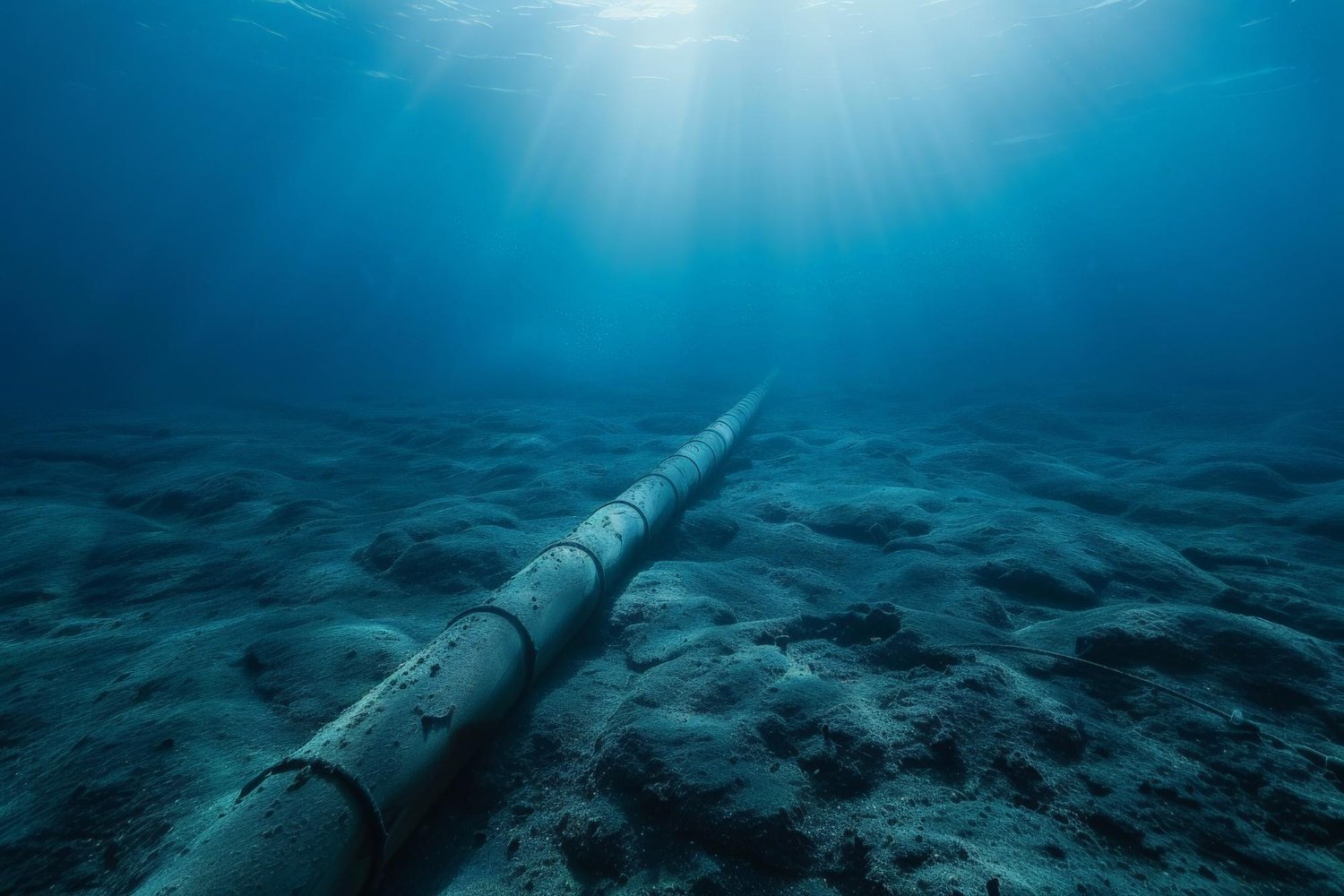
Australia’s Underwater Internet Cables: A Fragile Lifeline to the World
Australia’s global internet connectivity depends on just 15 underwater cables. These cables, vital to maintaining communication and data flow, are at risk of damage from external factors such as fishing activities, espionage, and natural disasters. Given their strategic importance, any disruption could have far-reaching consequences for both national security and economic stability. Recent concerns have…
-

CrowdStrike Crash Highlights the Intrusive Nature of Cybersecurity Software
The recent crash of CrowdStrike’s software has sparked concerns about the invasive nature of cybersecurity tools. While designed to protect, such software often has deep access to systems, raising privacy and performance issues. The incident calls into question whether there are better, less intrusive ways to secure systems without compromising functionality or privacy. Experts suggest…
-

Protecting NASA’s Spacecraft From Cyberattacks
NASA’s science mission spacecraft, which collect vital data for research, face growing cybersecurity risks. As space technology becomes more interconnected, these systems become increasingly attractive to hackers. A new U.S. law could help mitigate these threats by implementing stronger cybersecurity protocols, ensuring the safety of critical space infrastructure. The legislation aims to safeguard both governmental…
-

The Rise of Malicious AI: FraudGPT and the Next Frontier of Cyber Threats
As artificial intelligence advances, so do the methods cybercriminals use to exploit it. Dark large language models (LLMs) like FraudGPT and WormGPT have emerged, designed to facilitate criminal activities by generating malicious code, phishing campaigns, and undetectable malware. These tools, which operate without the ethical safeguards of regular AI, are promoted on the dark web,…
-

Mapping Cybercriminals’ Psychological Tactics: A New Model for Catching Online Scammers
Cybercriminals often use sophisticated psychological strategies to manipulate victims and gain access to sensitive information. A recent model developed by cybersecurity researchers combines data analysis and behavioral science to map these psychological games. By understanding the tactics scammers use, such as creating urgency or exploiting trust, experts can better predict, prevent, and combat these attacks….
-

Australian Port Cyberintrusion due to Unpatched Citrix Exploit
The recent cyber attack on a major Australian port operator – DP World Australia – highlights a critical cybersecurity issue stemming from a widely exploited Citrix vulnerability. This attack, which disrupted 40% of Australia’s shipping operations over a weekend, was attributed to Russian hackers exploiting a common Citrix flaw, leaving an estimated 30,000 shipping containers…
-

Cyberattack on DP World: Did It Put Australia’s Trade at Risk?
In a recent cyberattack on DP World, one of Australia’s major port operators, concerns were raised about the potential disruption to Australia’s trade and supply chain. While the attack caused temporary issues, experts believe that it has not significantly threatened Australia’s trade infrastructure this time. However, the incident highlights the increasing vulnerability of global supply…
-

Major Cyberattack on Australian Ports: Possible Sabotage by a Foreign State Actor
Recent reports suggest that a major cyberattack on Australia’s port infrastructure may have been an act of sabotage by a foreign state actor. This attack targeted key ports, potentially disrupting vital supply chains and trade routes. While the immediate impact was managed, the incident raises serious concerns about Australia’s national security and the vulnerability of…
-

What is Hybrid Warfare and the ‘Grey Zone’?
Hybrid warfare is a strategy that combines conventional military force with unconventional tactics such as cyberattacks, disinformation campaigns, economic pressure, and influence operations. It is often used to undermine an opponent without triggering a full-scale conflict, making it harder to detect and respond to effectively. This type of warfare operates in what is referred to…
-

Stuxnet Revisited: What We Can Still Learn About Infrastructure Cybersecurity
The Stuxnet computer worm, discovered in 2010, represents a watershed moment in the history of cybersecurity. Targeting Iran’s nuclear program, this sophisticated piece of malware was the first of its kind to cause physical damage to industrial equipment. A decade later, its implications still resonate, particularly as we witness an increasing number of cyber attacks…
