-

Australia’s Cyber Shield: A Bold Move to Fight Growing Online Threats
Australia’s digital systems are under constant pressure from skilled attackers who operate in stealth. Recent attacks have shown how easily networks — from government services to key industries — can be targeted and exploited. The country is no longer just reacting to threats; it’s stepping up with a clear, focused plan to stop them before…
-

Autonomous Weapons: A Growing Cybersecurity Threat
The rise of weapons that can choose and engage targets without human input marks a serious shift in how conflicts could unfold. These systems aren’t just military tools anymore—they’re being built into security setups like surveillance drones and automated border defenses. The real danger isn’t robots replacing humans in the field. It’s that mistakes, misjudgments,…
-
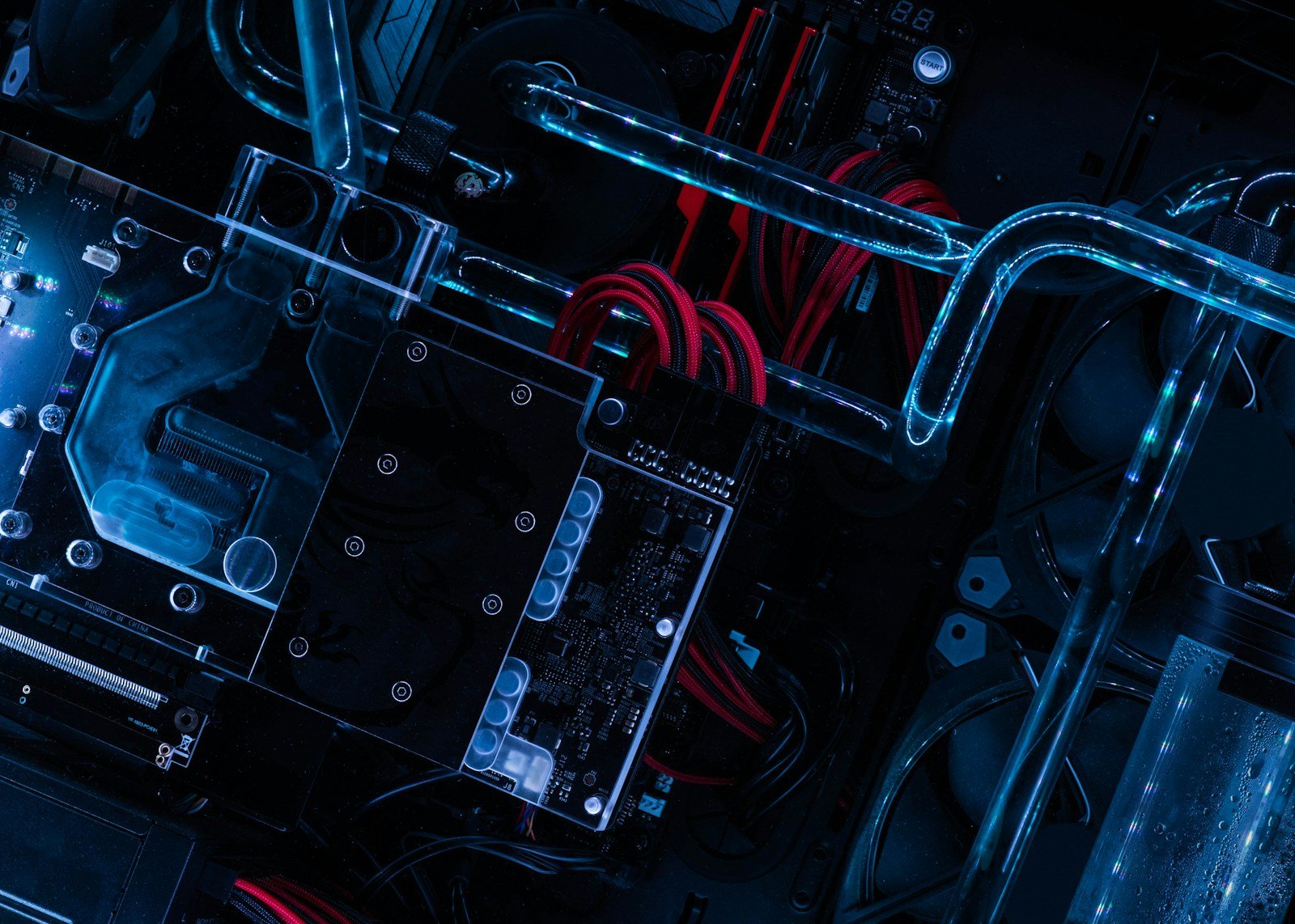
Quantum Leaps: Scaling Up Computing’s Potential – A Cybersecurity Perspective
The pursuit of vastly more powerful computers is driving significant innovation across numerous scientific and technological fields. While traditional computing continues to advance, the potential of quantum computing offers a radically different approach, promising solutions to complex problems currently intractable for even the most advanced supercomputers. This shift isn’t just about faster calculations; it represents…
-
Quantum Leaps: What Happens When Quantum Computers Grow Beyond the Lab
Quantum computing isn’t just about faster math—it’s a shift in how we handle information. Right now, most quantum systems are still in early stages, but progress is moving fast. The real issue isn’t just building more qubits; it’s keeping them stable. Quantum bits, or qubits, don’t act like regular bits. They can be both 0…
-

SMS 2FA: A Gateway for Cybercriminals
The security of online accounts relies on multiple layers of protection. While two-factor authentication (2FA) has become a standard defense mechanism, vulnerabilities persist within commonly used methods like SMS-based verification. Attackers are continually developing sophisticated techniques to bypass these safeguards, and one particularly alarming approach involves exploiting the way smartphones communicate with mobile network operators….
-

The Gray Zone: Understanding Hybrid Cyber Warfare
Cyberattacks are becoming a central element in geopolitical strategy. Sophisticated attacks targeting critical infrastructure and government systems aren’t solely the work of individual hackers; they represent a deliberate tactic designed to destabilize nations and achieve strategic goals. Recognizing the complexities of this new form of conflict is crucial for organizations and governments alike, demanding proactive…
-
SMS 2FA: Why It’s Still a Backdoor for Attackers
Two-factor authentication is meant to protect your accounts—yet too many services still rely on SMS for that extra layer. That’s a big problem. SMS messages are easy to intercept, manipulate, or even fake, and attackers are using those flaws every day. The real issue isn’t that two-factor auth is weak—it’s that the way SMS delivers…
-
The Hidden Front: How Hybrid Cyberattacks Are Reshaping Global Conflict
Cyberattacks aren’t just about hacking systems anymore. They’re part of a broader strategy to destabilize nations, erode public trust, and influence political outcomes. What used to be seen as isolated breaches is now a coordinated part of hybrid warfare—blending digital tactics with traditional military and political actions. These attacks target energy, water, transportation, and financial…
-

Silent Threats: How Sophisticated Spyware Operates
The ability to monitor communications and track device activity has become a serious concern for individuals and organizations alike. Recent investigations have revealed the use of highly advanced spyware – often referred to as “Pegasus” – by governments and potentially malicious actors to target specific individuals with alarming precision. These tools represent a significant risk,…
-
Cybersecurity: The Urgent Need for Collaborative Vulnerability Disclosure
The threat of cyberattacks is dramatically reshaping how we live and work. Data breaches impacting millions of individuals and organizations are becoming commonplace, exposing sensitive information and disrupting critical services. Recent events, including sophisticated ransomware attacks and targeted espionage campaigns, highlight the vulnerability of systems across all sectors – from government agencies to private businesses…
