-

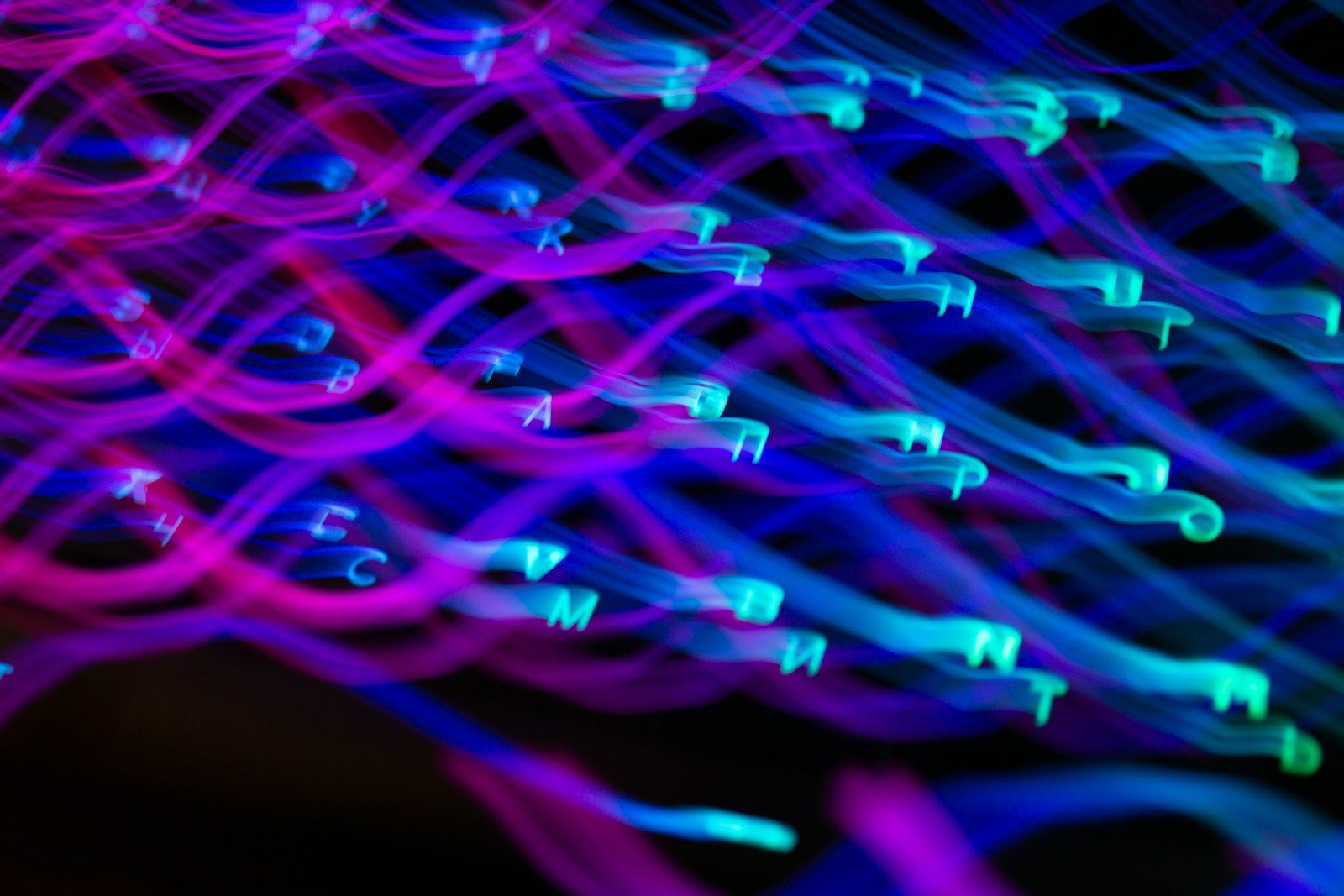
Understanding Ransomware: A Web of Criminal Actors
Ransomware isn’t just a technical glitch—it’s a coordinated operation that’s spreading across businesses and government systems. Attacks now involve a web of actors, each playing a role from the first scan of a network to the final demand letter. These groups don’t operate in isolation. Instead, they rely on a networked structure that spreads risk…
-

Mobile Apps: Why We Keep Letting Them See Too Much
Smartphones are full of apps—most of them doing more than just their basic jobs. They track where you are, who you talk to, what you click, and even your biometrics. Often, users don’t realize how much data is being collected or how it’s being used. The reality is that these apps build detailed profiles of…
-

Silent Surveillance: How Spyware Exploits Your Devices Without You Knowing
Spyware like Pegasus doesn’t just hide—it works silently. It can install itself on your phone without you ever clicking a link or opening a file. These attacks use zero-click vulnerabilities, meaning they trigger automatically when something happens on your device, like a missed WhatsApp call. No warning. No action needed. Once it’s in, the software…
-

Schools and Colleges Are Under Growing Cyber Attack
The shift to remote learning during the pandemic changed how schools operate — but it also opened the door for hackers. In 2020 and 2021, data breaches at schools and colleges spiked, with serious financial costs and real disruptions to teaching and learning. Schools often rushed to get students back online without fully assessing security…
-
Data’s Shadow: Do Tech Companies Really Own Their Responsibility?
Tech companies collect more data than ever—every click, every search, every purchase. That information isn’t just stored; it’s used to build profiles, target ads, and power decisions behind the scenes. The more data they gather, the more power they hold over people’s lives. Yet, the way this data is handled has come under fire. From…
-

Inside the Lines: How the Government Accessed Corporate Systems to Fight Cyberattacks
Federal agencies, most notably the FBI, recently gained direct access to private company servers to stop a wave of cyberattacks targeting Microsoft Exchange software. These attacks exploited unknown vulnerabilities—zero-day flaws—that allowed hackers to install remote control tools like web shells, giving them full access to sensitive data. The attacks spread fast across dozens of organizations,…
-

Protecting Student Data in Online Learning: What’s Really at Stake
When schools moved to remote learning during the pandemic, they did so quickly—often without fully planning how students’ data would be handled. Students weren’t just logging into platforms; they were being tracked. Every video call, every assignment submitted, every click in a learning app generates data. That data is collected, stored, and sometimes shared—often without…
-

Digital Credentials: Building Trust in a Post-Pandemic World
As societies reopen, digital vaccination passports are being used to verify immunity—offering a way to balance public health goals with personal freedom. But behind the scenes, these systems carry real cybersecurity risks. If a system stores health data in a central location, it becomes a prime target. Once breached, the consequences could be severe Getting…
-

The Hidden Cost of Your Data: What Cybercriminals Do With It
When data gets stolen, it doesn’t vanish. It goes somewhere else—into the hands of people who don’t care about your privacy. The fallout from a breach isn’t just about lawsuits or public apologies. What really matters is what happens to that data after it’s taken. Cybercriminals don’t just use it for scams. They sell it,…
-

Guardians in the Sky and Below: How Cyber Threats Are Spreading Into Space and Ground Systems
We’re now living in a world where technology doesn’t stop at our screens or servers—it reaches into space. Satellites, power grids, water systems, and pipelines all depend on digital networks that span Earth and orbit. When hackers or state actors target one of these systems, the damage doesn’t stay contained. A jammed GPS signal or…
