-

Cyberwarfare: How Attacks on Power and Data Could Unravel Modern Society
Cyberwarfare isn’t just a plotline in a movie anymore. Real actors—some with political or economic motives—are building tools that can shut down vital services. The energy grid is a top target because when power goes out, everything else falters The digital world runs on interconnected systems, and that interdependence means one failure can grow into…
-

Cyber Conflict: The Hidden Danger and How to Respond
We’re already living in a world where digital attacks can bring entire systems to a halt. From hospitals to power grids, critical infrastructure is being targeted more often and with greater precision. These aren’t just technical glitches—they’re deliberate actions meant to disrupt society. What’s worse is that most responses still rely on patching holes after…
-

Cyber Espionage: When Retaliation Isn’t Always the Answer
Cyberattacks are no longer rare. They’re happening more often, targeting everything from universities to private companies, and the damage can be massive. A recent investigation uncovered a campaign that compromised over 100,000 academic accounts, reached around 8,000 email addresses, and stole research data worth nearly $3.4 billion. The attackers didn’t just break in—they used tactics…
-
Shadow Networks: The Real Enemy Isn’t the Tools — It’s the People Behind Them
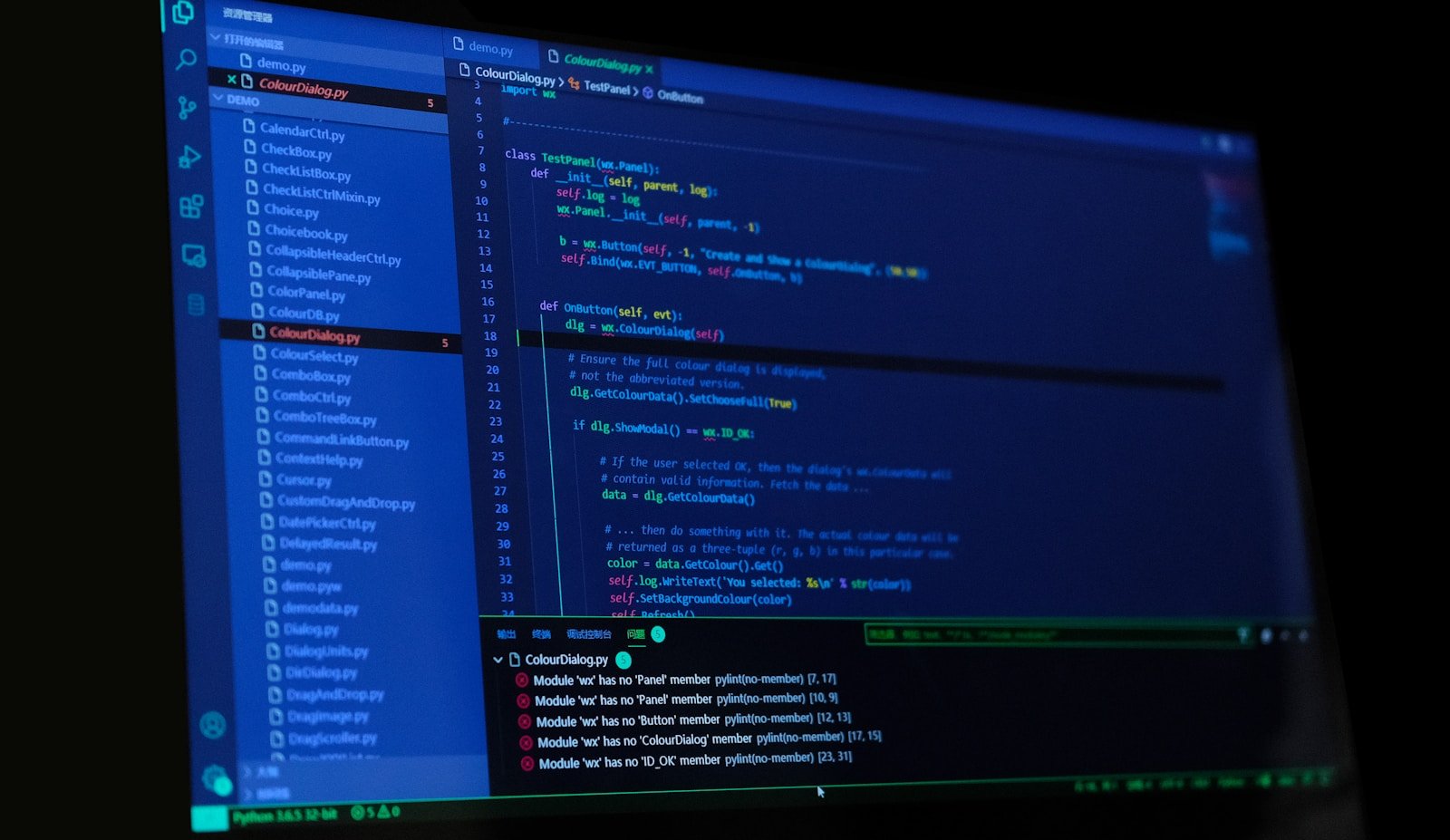
Cyberattacks are getting smarter and more common. Governments are pushing hard to control weaponized hacking tools and known software flaws. But what’s being missed is how much the real danger lies in the people who use that knowledge. It’s not just about having access to advanced software. It’s about who can deploy it — the…
-

Cybersecurity: How We Fight Back Against Evolving Threats
Cyberattacks are no longer rare or isolated. They’re happening more often, targeting everything from power grids to personal data. From state-backed groups to organized crime, attackers are finding new ways to exploit weaknesses—sometimes without even needing deep technical skills. These aren’t just about causing chaos. They’re about breaking trust, stealing money, and influencing outcomes on…
-

Building a Digital Shield: Why Deterrence Works Better Than Reaction
Cyberattacks are no longer rare or isolated—they’re happening more often, targeting everything from power grids to personal data. Recent attacks on critical systems and large-scale malware campaigns show how fast and deep these threats can go. We’ve been relying on reacting after breaches happen, but that doesn’t stop the next wave. Real protection starts before…
-

Silent Sentinels: The Hidden Dangers in Everyday Connected Devices
We’re surrounded by smart devices—fitness trackers, smart speakers, baby monitors, home security cameras—each promising to make our lives easier. But behind that convenience lies a quiet danger. These devices often come with weak security by default. They don’t need to be hacked to be risky. Many just ship with default passwords, no encryption, and outdated…
-

Sophisticated Deception: How Nation-State Actors Play the Game of Trust with Cybersecurity Pros
Cybersecurity pros are being targeted not just with malware or phishing links—but with believable, well-crafted lies that look like they come from trusted sources. A recent campaign by North Korean hackers shows how these actors aren’t just stealing data or breaking into systems. They’re creating fake social media profiles that mimic ethical hackers, posting detailed…
-
Silent Threats in Orbit: Keeping Our Satellites Safe
Satellites are now more common than ever — thousands more are heading into orbit over the next decade. Projects aim to bring internet access to remote areas and improve environmental monitoring, which is great. But with that growth comes a serious cybersecurity problem. These systems rely heavily on off-the-shelf parts and software, often skipping deep…
-

Cyberattacks: How Digital Threats Are Reshaping Global Security
We’re living in a world where the most dangerous threats aren’t always on battlefields or in nuclear arsenals. They’re in the code that powers our cities, our water, and our energy. Cyberattacks aren’t just about stealing data anymore. They can shut down power grids, poison water supplies, or bring entire industrial systems to a halt….
