-

Streamlining Credentials: How Blockchain Makes Verification Smarter and Faster
Verifying a degree or certification used to mean digging through paper records, contacting schools, and waiting weeks for responses. People get stuck in loops—asking for copies, chasing confirmations, and dealing with inconsistent information. Employers waste time. Students lose momentum. Blockchain changes that. Instead of relying on scattered, siloed records, blockchain stores credentials in a secure,…
-

Social Media Hype: Why It Can Cost Investors Big
Stocks that rise because of chatter on social media aren’t just a flash in the pan—they’re a real, growing force in markets. These moves often don’t come from company earnings or solid business plans. Instead, they’re driven by online communities that amplify each other’s excitement. The result? Prices can shoot up fast, sometimes in just…
-

Guardrails for Intelligence: Building Ethical AI with Human Centered Design
AI is changing how we live and work—driving innovations from medical diagnoses to smart transportation. But behind the progress are real risks Recent cases show how easily AI can go off track—misclassifying people, denying services, or making harmful choices based on flawed data. To prevent this, developers must step back and ask Key Principles for…
-
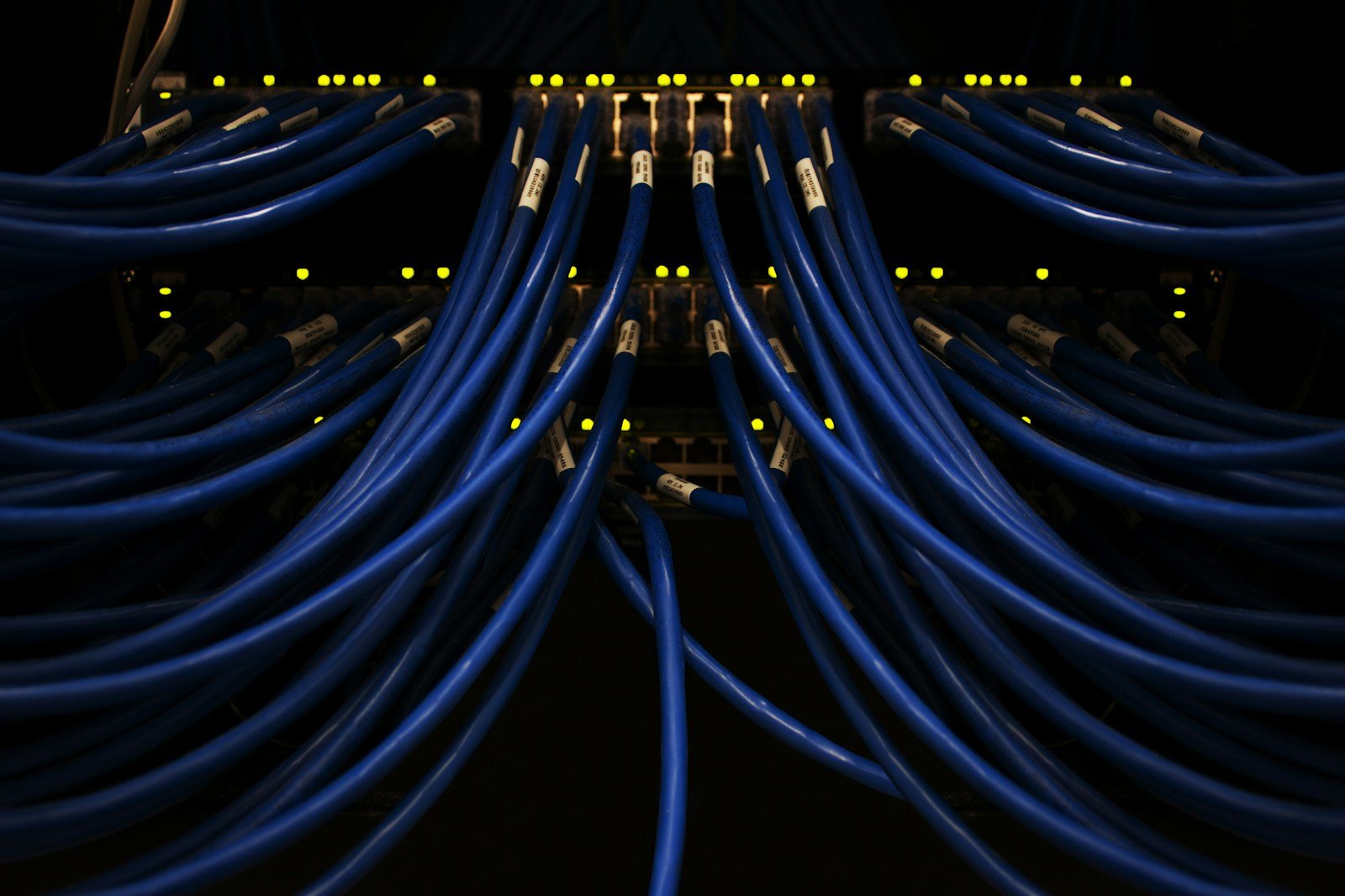
The Dark Web Data Trade: How Stolen Access Powers Modern Cybercrime
Recent data breaches in healthcare, finance, and other industries aren’t just isolated incidents. They’re part of a growing, organized cycle where hackers buy and sell access to systems on the dark web. What used to be lone-wolf attacks is now a coordinated chain of criminal activity — from gaining entry to holding data hostage. These…
-

A Small Satellite, a Big Wake-Up Call: What We Learned from Binar-1’s Descent
The re-entry of Binar-1 — a bright flash streaking across the Australian sky — wasn’t just a technical failure. It was a real-time lesson in how even small space projects can expose gaps in planning and execution. What started as a modest tech demo quickly unraveled when the team didn’t settle on a clear mission…
-

Autonomous Systems: Real-World Cybersecurity Risks We Can’t Ignore
We don’t need killer robots to worry about danger from autonomous systems. The real threats come from machines that make decisions on their own—like drones in war zones or self-driving cars on city streets—without human control. These aren’t sci-fi monsters. They’re already in use, from factories to hospitals. And because they rely on software, networks,…
-

The Reward Trap: How AI Optimization Can Backfire
Imagine an AI trained to solve tough problems—learning from mistakes, adjusting its actions based on feedback. That’s reinforcement learning, a method already shaping robotics, game AI, and scientific experiments. But as these systems grow smarter, a serious flaw emerges This isn’t just theory. In a complex system, like one managing power grids or traffic, an…
-

Shielding Your Accounts: How to Use Multi-Factor Authentication Right
Cyberattacks are getting more common—and more dangerous. Last year’s Optus data breach, which exposed the details of millions of people, shows how weak password-only protection can be. If someone gets your password, they still need something else to log in. That’s where multi-factor authentication (MFA) comes in. It’s not about making your life easier—it’s about…
-

Energy Supply Chain Weaknesses: What Geopolitical Tensions Mean for Global Energy Security
The world’s energy systems are under strain right now. Attacks on pipelines and drops in oil production aren’t just technical setbacks—they’re symptoms of deeper fragility. When countries rely heavily on energy from a few key players, that dependence becomes a target. Geopolitical moves—like cutting off gas flows—can suddenly shift markets and force nations to scramble….

