-
Spotting the Red Flags: How to Spot Fake Emails Before They Hack You
A single email can ruin your day—or your finances. Scammers are getting smarter, crafting messages that look real, sound urgent, and come from people you trust. They don’t just want your password—they want you to act, to panic, to click. And most of us don’t notice the small things that make it fake. A misspelled…
-

Critical Infrastructure: Still Too Fragile to Protect
The systems that keep our cities running—power grids, water treatment, transportation—aren’t just behind glass walls or firewalls. They’re the backbone of daily life. And yet, they’re still sitting ducks for cyberattacks. These aren’t just IT systems. They’re physical networks that control everything from how water flows to how power gets delivered. When one part fails,…
-
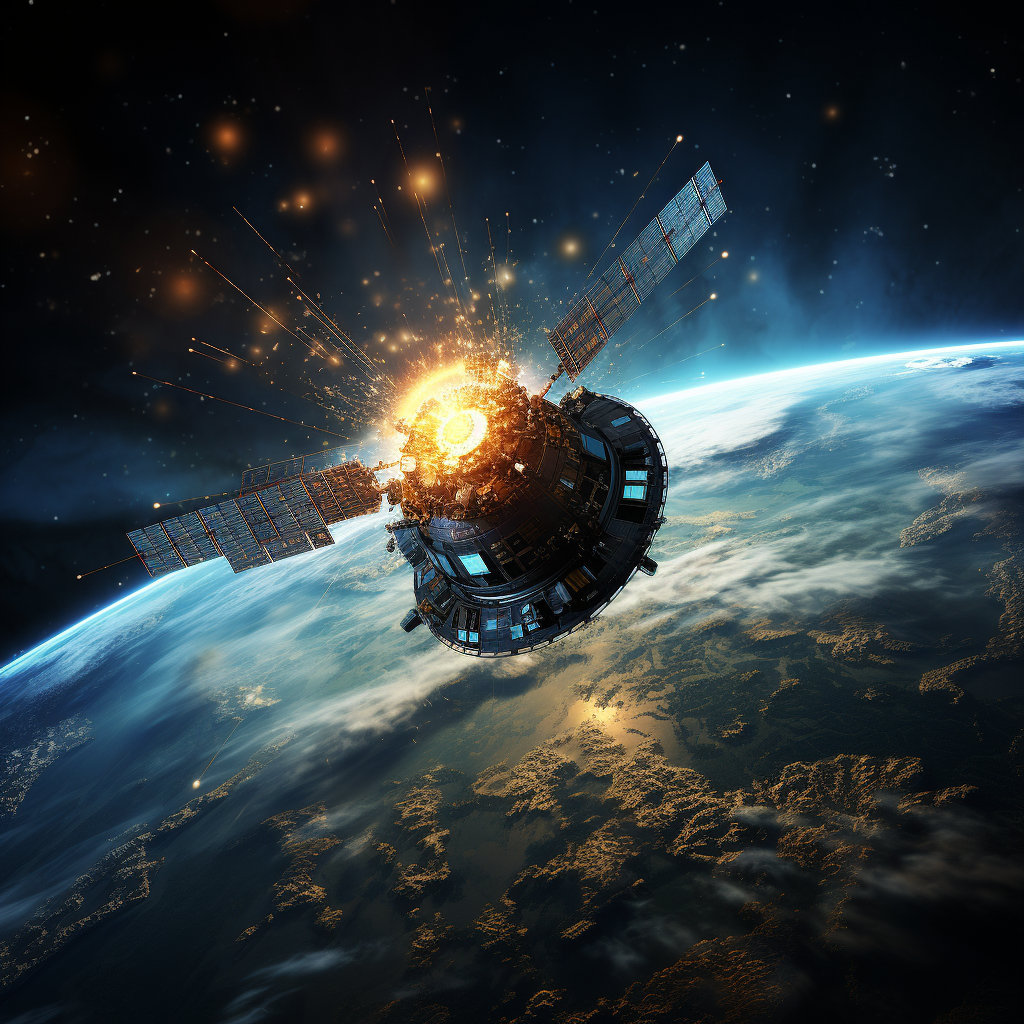
The Eyes in the Sky: How Satellites Are Changing the Way Wars Are Fought
The war in Ukraine has made it clear that satellites aren’t just tools for monitoring — they’re now central to how battles are fought. Ukrainian forces have used commercial satellites to see what’s happening on the ground in real time, even under clouds or at night. This access to high-resolution imagery lets them track troop…
-

The Ghost in the Machine: How Fiction Exposes Real Cybersecurity Weaknesses
Cyberattacks don’t always come from the outside. Sometimes, the real threat is someone already inside the system—someone with access, trust, and a quiet way of working. Shows like *Star Trek The danger isn’t just about hackers with tools. It’s about people—employees, contractors, even partners—who can open doors without raising alarms. When someone inside has access,…
-

The Quiet Shift: How Artificial Intelligence is Changing Global Security
For years, intelligence agencies have worked behind the scenes, sifting through mountains of data to spot threats and protect national interests. Today, artificial intelligence is stepping into that role—not just as a helper, but as a core part of how security decisions are made. The sheer amount of information flowing in from social media, satellites,…
-

AI in the Hands of Cybercriminals: How Bad Actors Are Using It
Cybercriminals are no longer just writing scripts or sending generic emails. They’re now using AI tools to make scams more believable, faster, and harder to spot. From crafting phishing messages that sound like they come from a real person to impersonating bank agents or family members over the phone, these attacks are getting sharper and…
-

Supply Chain Attacks: How Threats Are Now Targeting the Web of Trust
Recent attacks on big names like British Airways, the BBC, and Boots show a clear shift in how hackers operate. Instead of just locking down data with ransomware, they’re now going after the trusted partners that run day-to-day operations. When a supplier is compromised—like the software company Zellis—attackers don’t just grab data. They use that…
-

The Silent Threat: How Cars Are Being Hacked – And What You Can Do About It
Cars aren’t just machines anymore. They’re packed with sensors, software, and connectivity that make them smarter, safer, and more convenient. But that same tech is opening doors for hackers. From keyless entry to remote diagnostics, modern vehicles are now accessible points for bad actors. The rise in thefts of cars with advanced features isn’t just…
-

Healthcare on the Brink: Cyberattacks Are Disrupting Patient Care and Safety
Hospitals and medical facilities are being targeted like never before. Recent attacks show a clear shift—cybercriminals aren’t just stealing data anymore. They’re hitting systems that control daily operations, from scheduling to life-saving equipment. The Crown Princess Mary Cancer Centre was taken over by a group known as Medusa, who locked down its systems and threatened…
-

The Quantum Threat: Why Our Data Might Be at Risk Soon
Our current digital security relies on math problems that are nearly impossible for regular computers to solve—like factoring huge numbers into primes. That’s what keeps bank transactions, passwords, and private messages safe today. But quantum computers are changing the game. They don’t just crunch numbers faster—they work differently, using quantum bits or qubits to perform…
